Stealing and faking Azure AD device identities
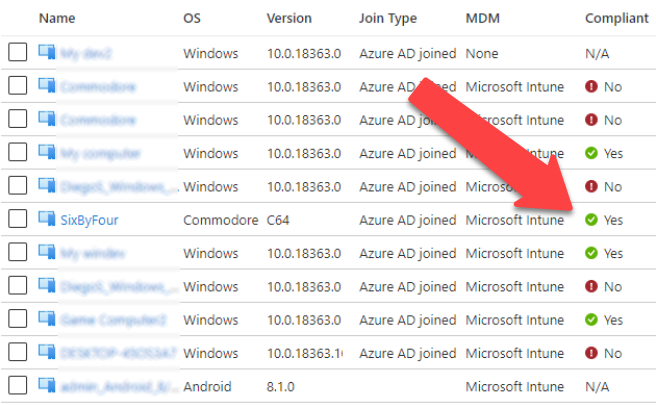
In my previous blog posts I’ve covered details on PRTs, BPRTs, device compliance, and Azure AD device join.
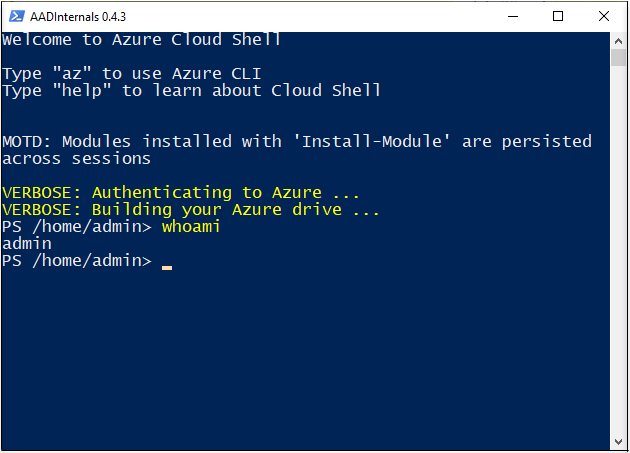
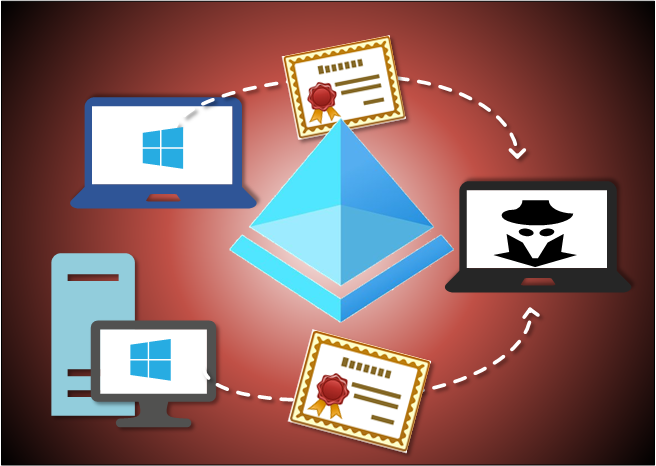
In this blog, I’ll show how to steal identities of existing Azure AD joined devices, and how to fake identies of non-AAD joined Windows devices with AADInternals v0.6.6.