AAD Kill chain
Introduction
According to Verizon’s Data Breach Investigations Report 2020, externals attackers are considerable more common than internal attackers. In the cloud era, attacking the organisation from the outside is much more difficult, if not impossible. Therefore, to be able to access organisation’s data, one must gain some level of legitimate access to the organisation.
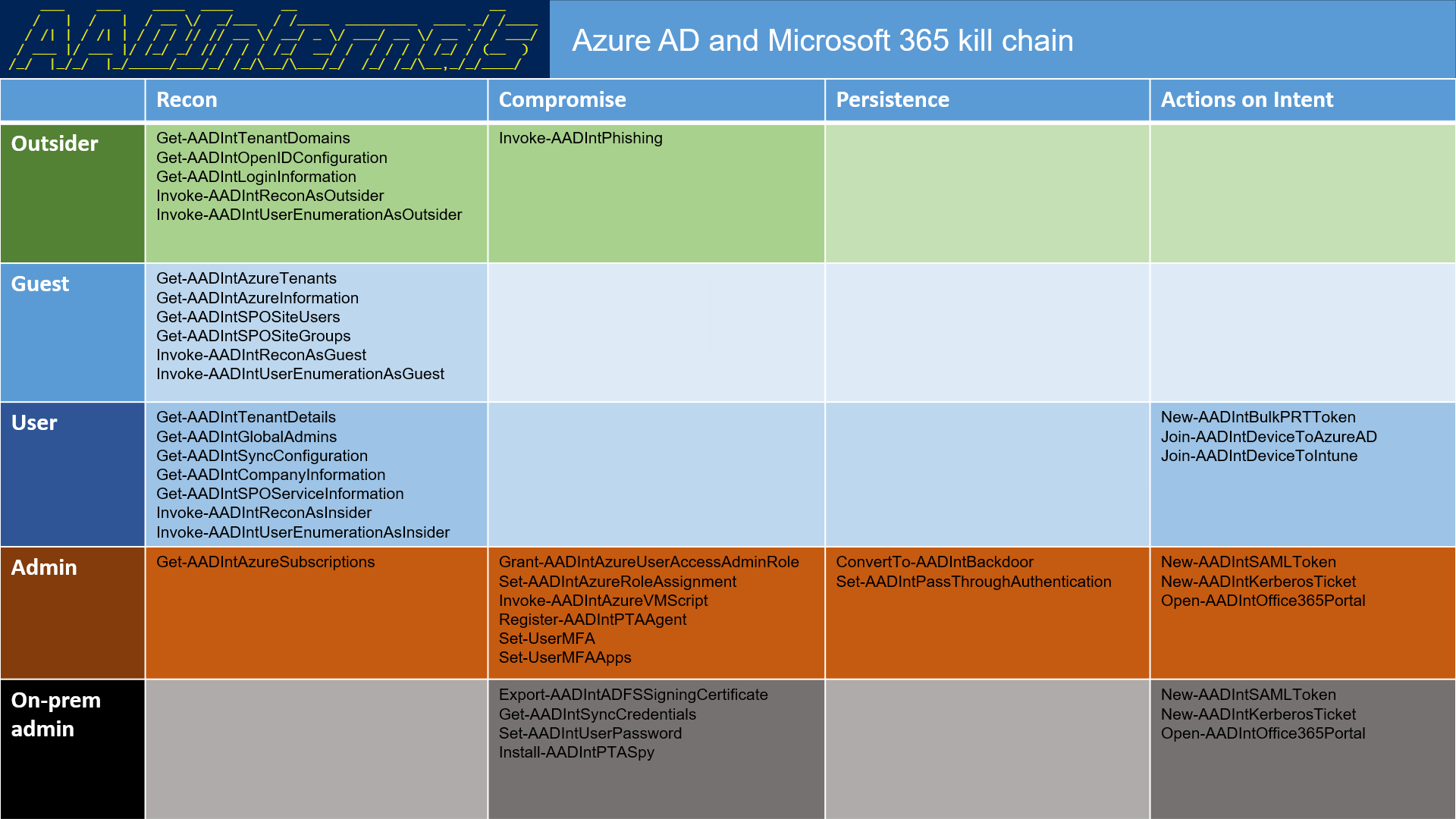
The Azure AD and Microsoft 365 kill chain is a collection of recon techniques and hacking tools I’ve discovered and built during the last 10+ years while working with Microsoft cloud services.
Kill chain roles
The kill chain consists of five different roles: outsider, guest, insider, admin, and on-prem admin. Typically, outsiders are aiming for guest, insider, or admin roles. Similarly, guests are aiming for insider or admin roles. Insiders can already do much harm, but to get “keys to the kingdom” they often are aiming for (cloud) admin role. This is same for the on-prem admin.
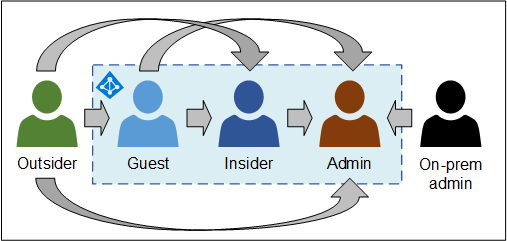
Figure 1: Azure AD Kill Chain roles and target
Attackers’ ultimate goal is to get access to target tenant. The kill chain provides tools for recon to improve targeting the organisation. After gaining the preferred role (out-of-scope of kill chain), the kill chain provides tools for hacking the organisation.
Outsider
Outsider refers to an user who has no access to the tenant of the target organisation.
Outsiders can exract information from any tenant using publicly available APIs and DNS queries. See the blog post for more details.
The ultimate goal of an outsider is to gain guest, user, or admin role.
Guest
Guest refers to an user who has guest access (external user) to the target tenant. These users have a restricted access to Azure AD, but they can gather a lot of information from tenant using various APIs provided by Microsoft. For instance, guests can easily read the whole Azure Active Directory (AAD) using MS Graph API.
See the blog post for more details.
User (insider)
User refers to “normal” users of the tenant. They have read-only access to practically all information in AAD. However, users are also able to invoke Denial-of-Service (DoS) attacks against their own tenant by filling the Azure AD with user or device objects, making it practically unusable.
See the blog post for more details.
Admin
Admin refers to a Global Administrator role. Global admin has an unlimited access to all settings in the tenant. As such, they can change security settings, access any data, and create back doors.
See the blog post for more details.
On-prem admin
On-prem admin refers to an administrator who is administering on-prem servers running Azure AD Connect, Active Directory Federation Services (AD FS), or Active Directory.
On-prem admins doesn’t have direct access to the cloud, but they can dump Azure AD Connect credentials and gain admin rights to cloud.
If organisation is using Desktop SSO (also known as Seamless SSO), on-prem admin can dump the MD4 hash of AZUREADSSO computer account password and create Kerberos tickets to login as any user of the tenant.
Similarly, If organisation is using identity federation, on-prem admin can export the token signing certificates and sign in as any user of the tenant and bypass MFA!
See the blog post for more details.
