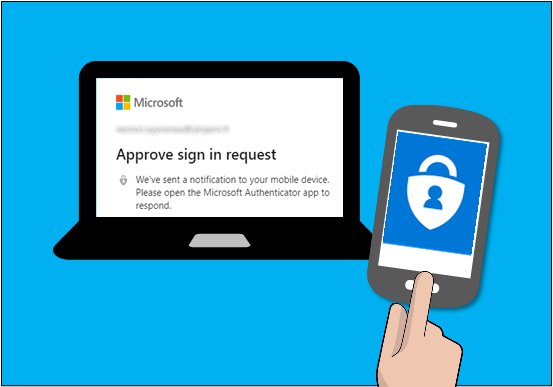
Multi-factor Authentication (MFA) and Conditional Access (CA) policies are powerful tools to protect Azure AD users’ identities.
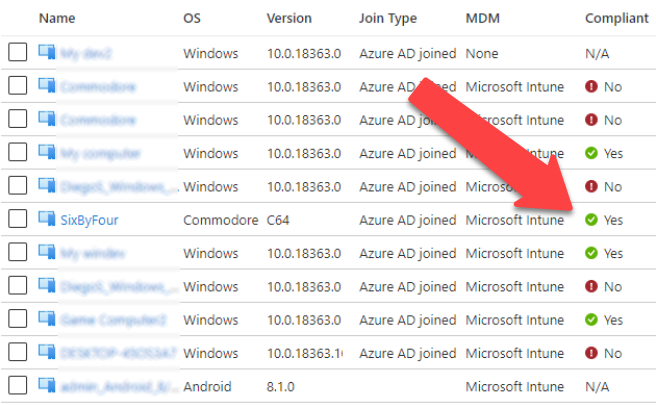
For instance, one may allow access only from compliant devices and require MFA from all users.
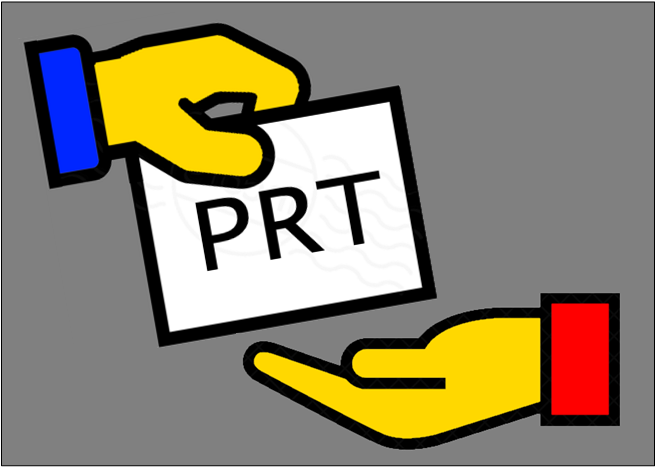
However, because of Azure AD authentication platform architecture, users can bypass home tenant MFA and CA policies when logging in directly to resource tenants.
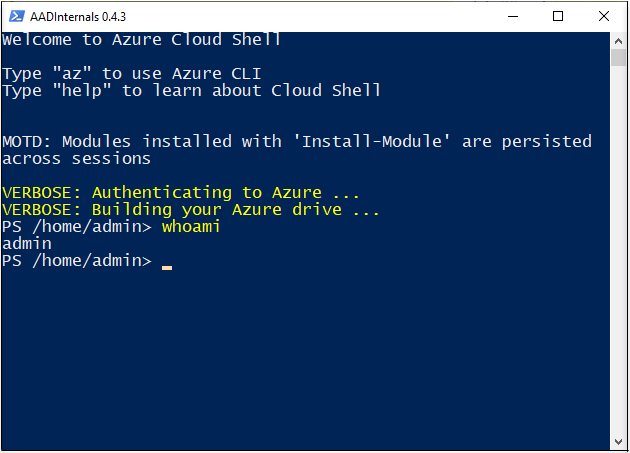
This blog post tries to shed some light on how Azure AD authentication works under-the-hood.
We’ll introduce the issue, describe how to exploit it, show how to detect exploitation, and finally, how to prevent the exploitation.
The blog is co-authored with @SravanAkkaram and is based on his findings.